Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys
Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys

Rapid7's Impact from Apache Commons Text Vulnerability (CVE-... - vulnerability database | Vulners.com
Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys
Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys
GitHub - s1ckb017/PoC-CVE-2022-26809: PoC for CVE-2022-26809, analisys and considerations are shown in the github.io.
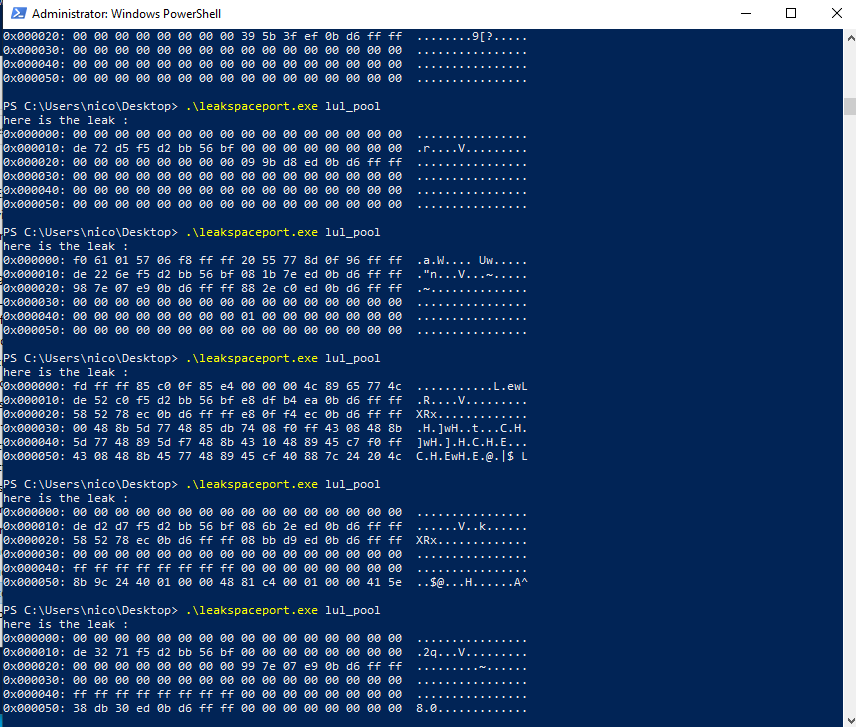
GitHub - Big5-sec/cve-2022-21877: a demonstration PoC for CVE-2022-21877 (storage spaces controller memory leak)
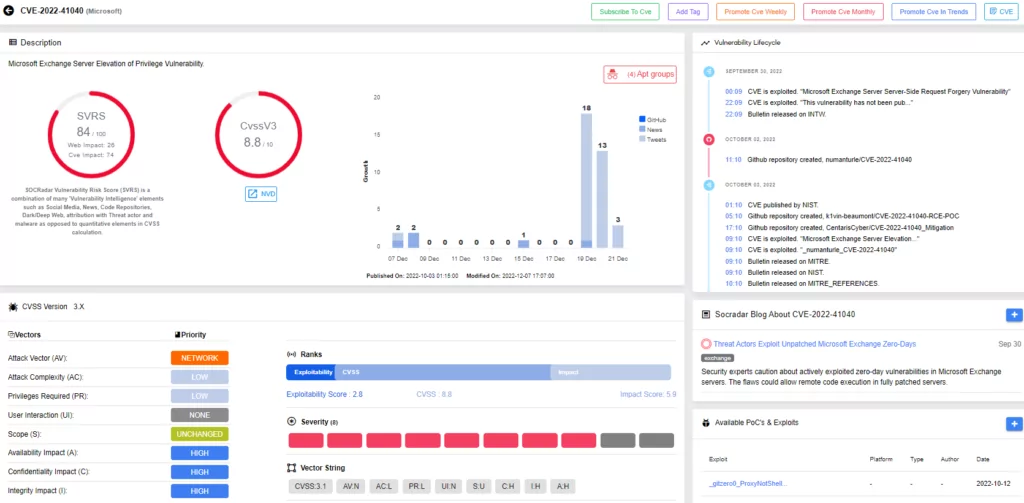
Reports of ProxyNotShell Vulnerabilities Being Actively Exploited (CVE-2022-41040 and CVE-2022-41082)
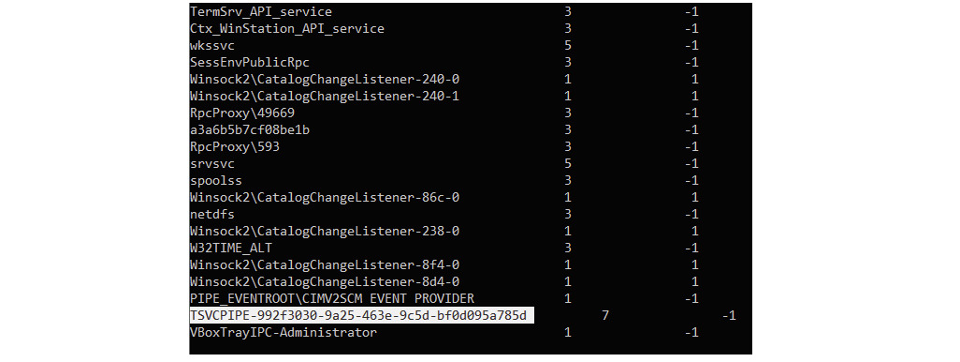
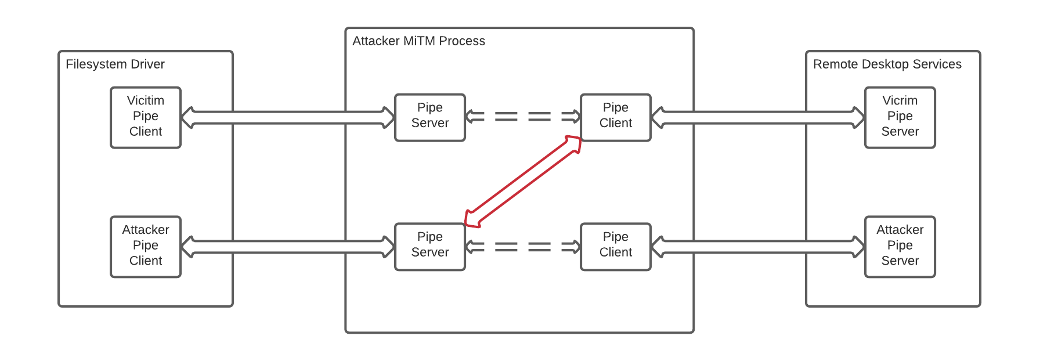
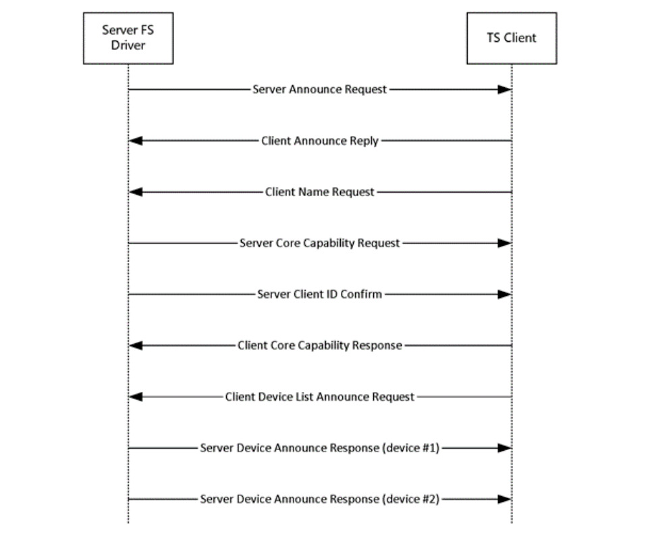
Attacking RDP from Inside: How we abused named pipes for smart-card hijacking, unauthorized file sys

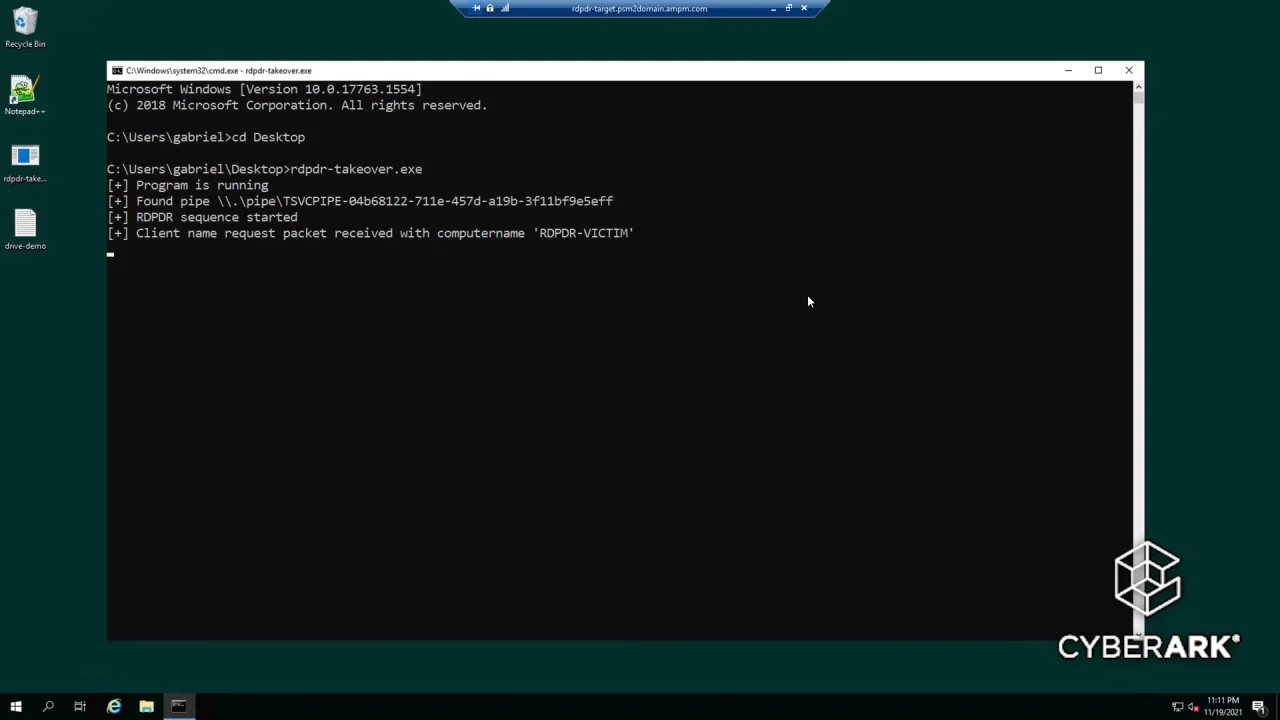
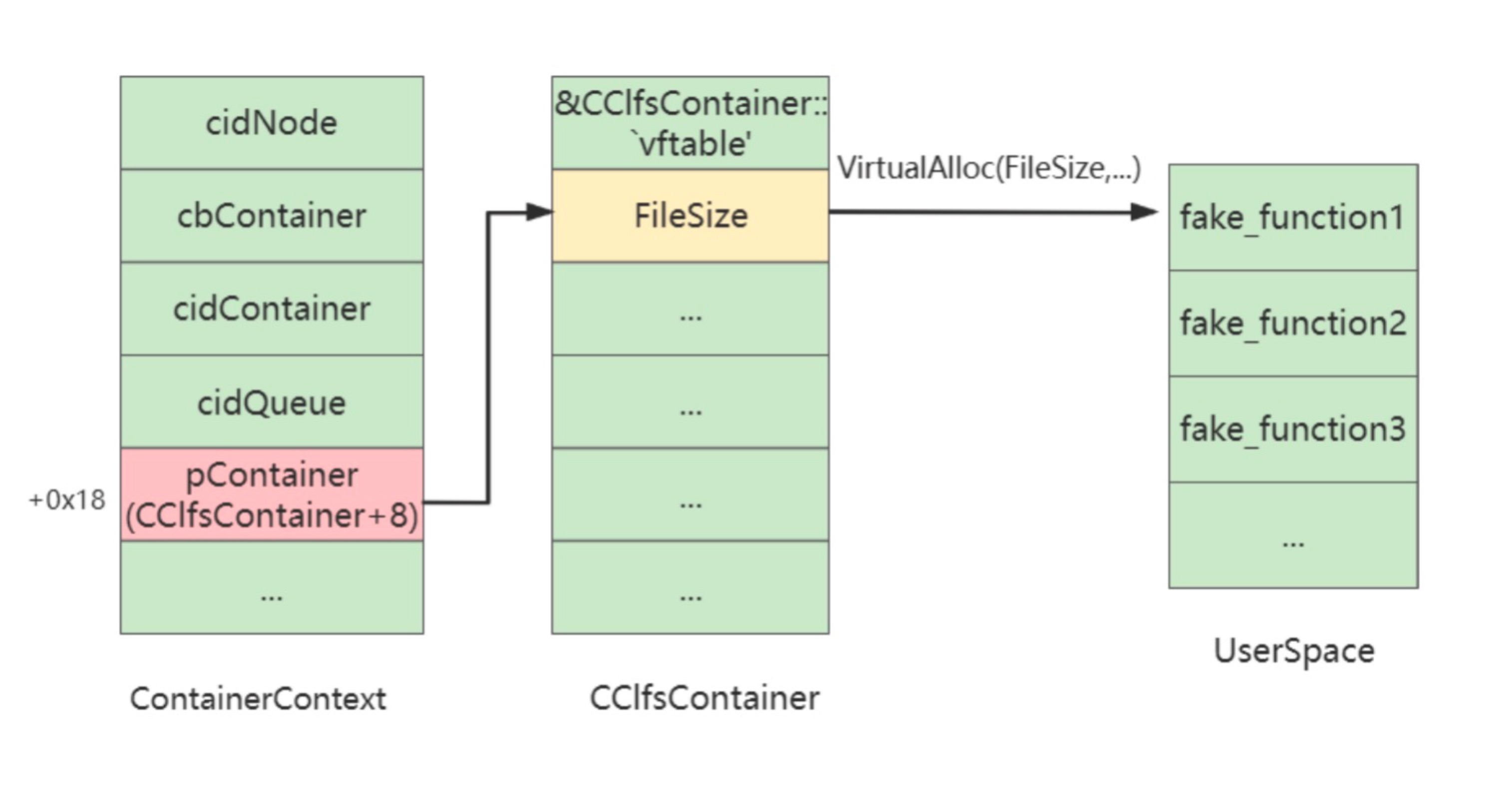
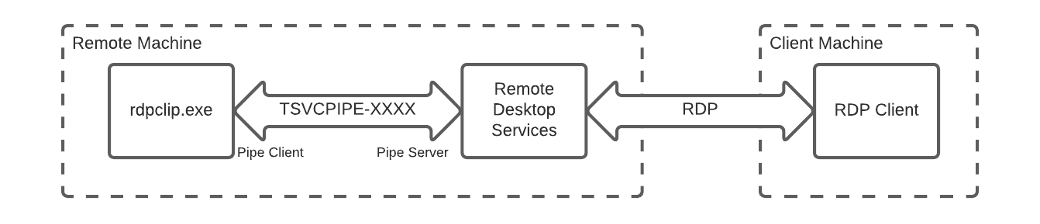
Remote Desktop Protocol Remote Code Execution Vulnerability – CVE-2022-21893 - Security Investigation