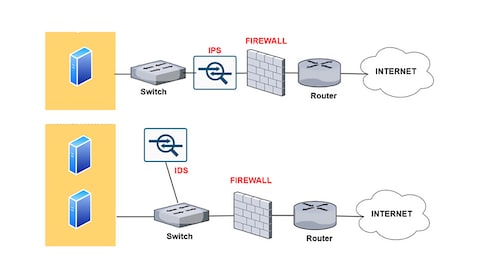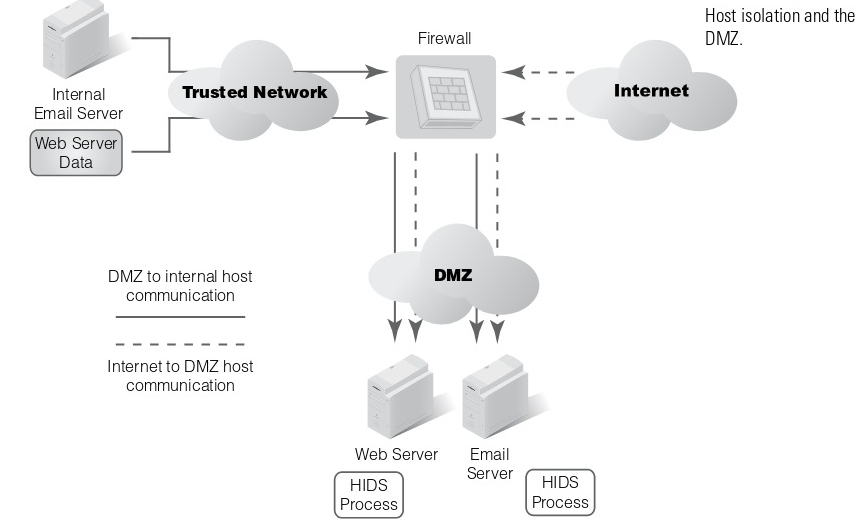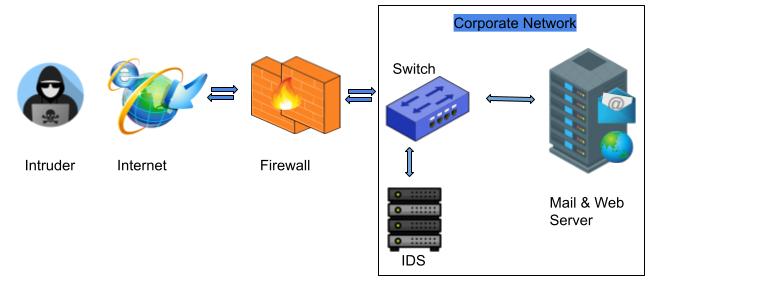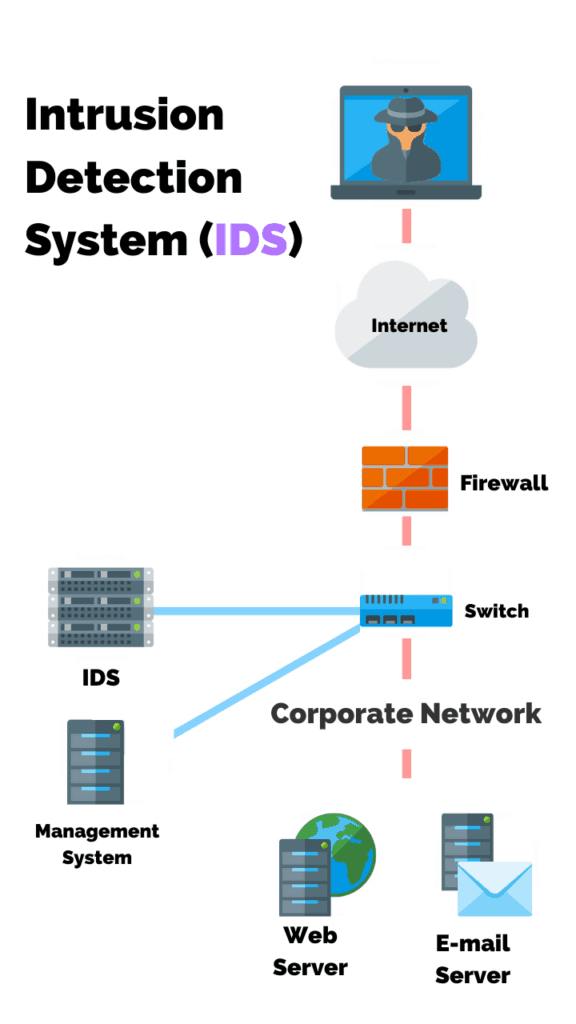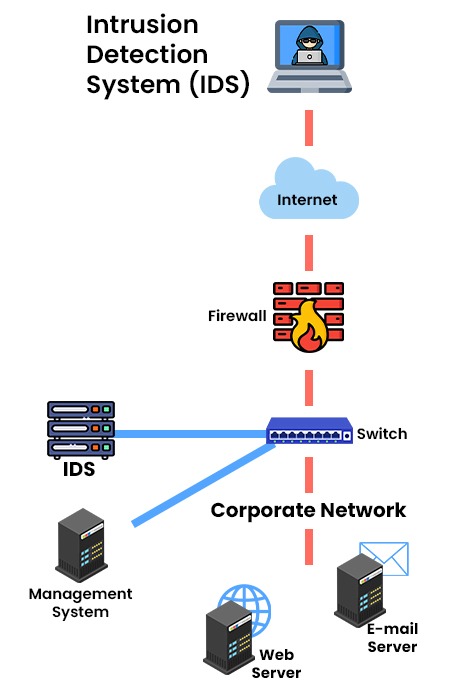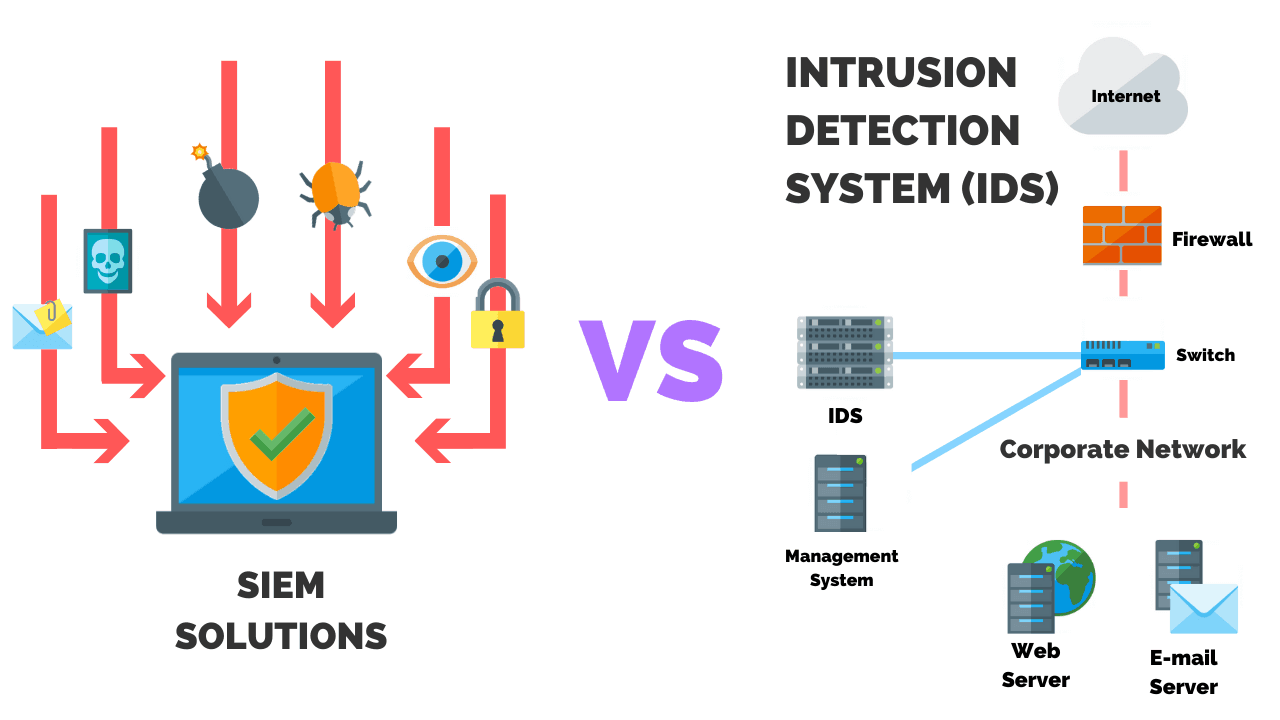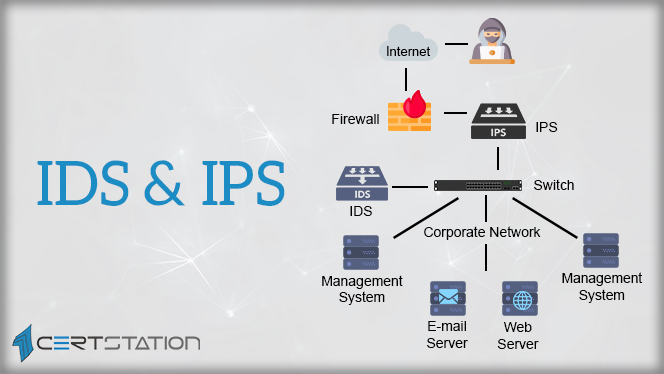
A Detailed Analysis of Intrusion Detection Systems and Intrusion Prevention Systems - CERTStation Blog
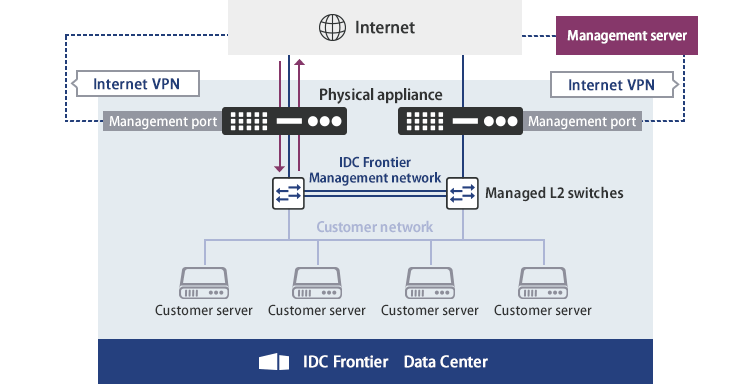
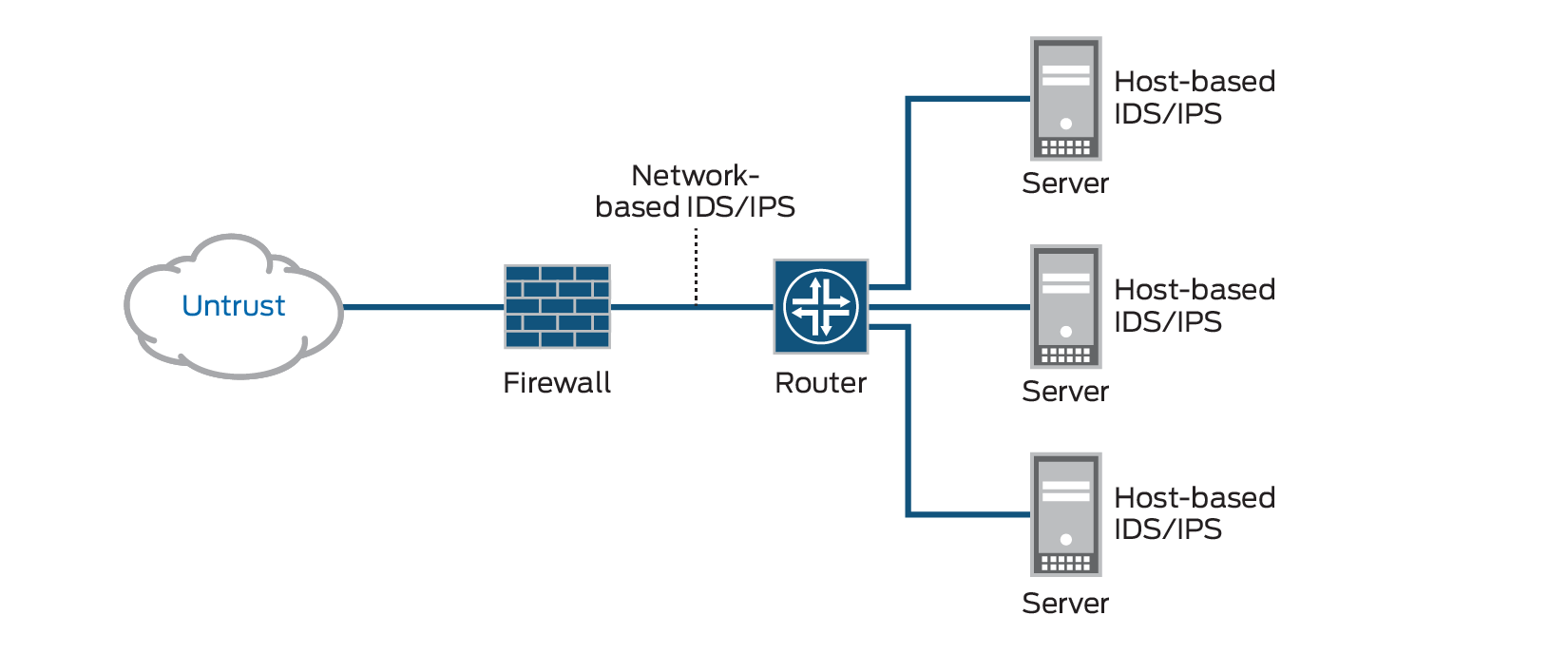
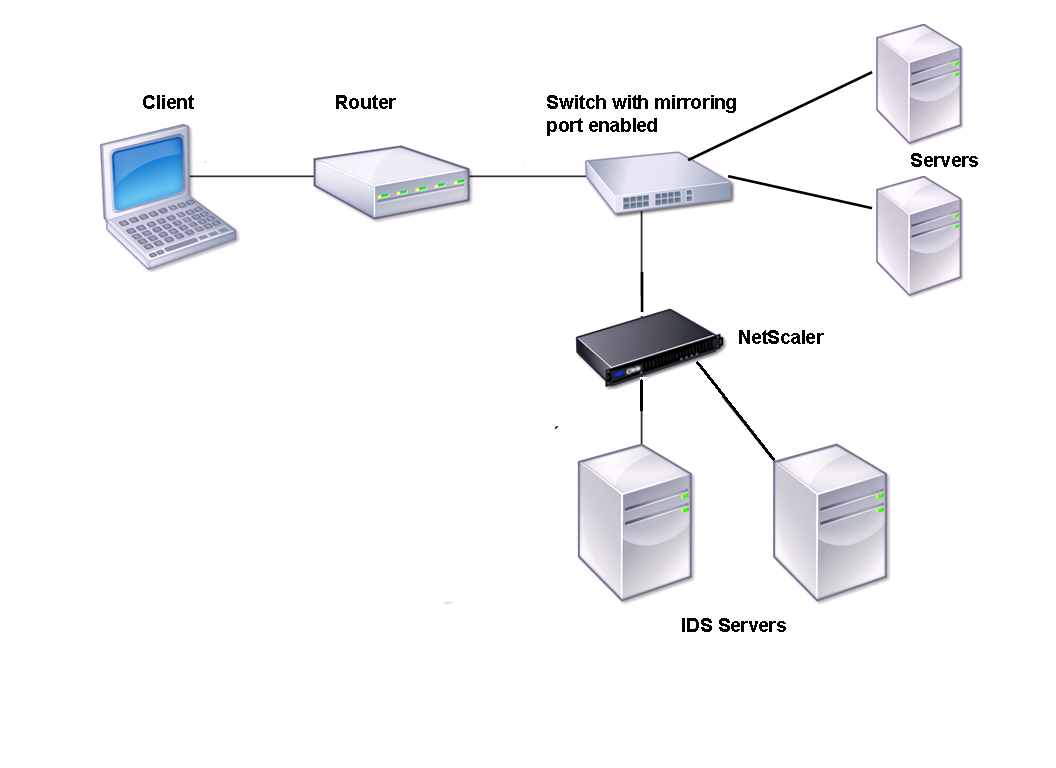
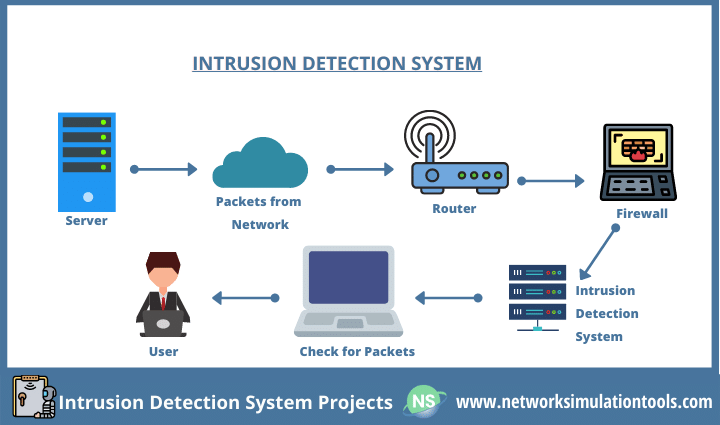
Intrusion Detection System/Intrusion Prevention System Service (IDS/IPS)|IDC Frontier's Data Centers

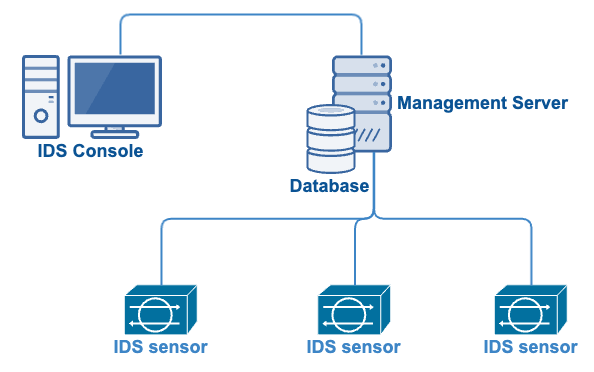
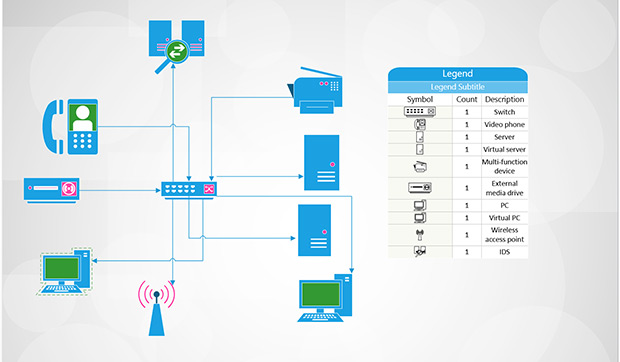
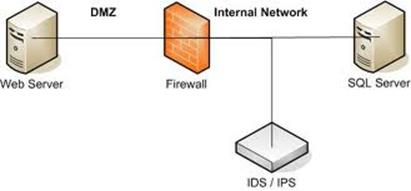
Figure 4 from Intrusion Detection System (IDS) server placement analysis in cloud computing | Semantic Scholar